Cybercriminals and spies working for nation-states are surreptitiously coexisting inside the identical compromised name-brand routers as they use the units to disguise assaults motivated each by monetary achieve and strategic espionage, researchers mentioned.
In some circumstances, the coexistence is peaceable, as financially motivated hackers present spies with entry to already compromised routers in change for a charge, researchers from safety agency Development Micro reported Wednesday. In different circumstances, hackers working in nation-state-backed superior persistent menace teams take management of units beforehand hacked by the cybercrime teams. Typically the units are independently compromised a number of occasions by completely different teams. The result’s a free-for-all inside routers and, to a lesser extent, VPN units and digital personal servers offered by internet hosting corporations.
“Cybercriminals and Superior Persistent Menace (APT) actors share a standard curiosity in proxy anonymization layers and Digital Non-public Community (VPN) nodes to cover traces of their presence and make detection of malicious actions harder,” Development Micro researchers Feike Hacquebord and Fernando Merces wrote. “This shared curiosity leads to malicious web visitors mixing monetary and espionage motives.”
Pawn Storm, a spammer, and a proxy service
A very good instance is a community made up primarily of EdgeRouter units offered by producer Ubiquiti. After the FBI found it had been contaminated by a Kremlin-backed group and used as a botnet to camouflage ongoing assaults focusing on governments, militaries, and different organizations worldwide, it commenced an operation in January to quickly disinfect them.
The Russian hackers gained management after the units had been already contaminated with Moobot, which is botnet malware utilized by financially motivated menace actors not affiliated with the Russian authorities. These menace actors put in Moobot after first exploiting publicly identified default administrator credentials that hadn’t been faraway from the units by the individuals who owned them. The Russian hackers—identified by a wide range of names together with Pawn Storm, APT28, Forest Blizzard, Sofacy, and Sednit—then exploited a vulnerability within the Moobot malware and used it to put in customized scripts and malware that turned the botnet into a world cyber espionage platform.
The Development Micro researchers mentioned that Pawn Storm was utilizing the hijacked botnet to proxy (1) logins that used stolen account credentials and (2) assaults that exploited a essential zero-day vulnerability in Microsoft Alternate that went unfixed till March 2023. The zero-day exploits allowed Pawn Storm to acquire the cryptographic hash of customers’ Outlook passwords just by sending them a specifically formatted e mail. As soon as in possession of the hash, Pawn Storm carried out a so-called NTLMv2 hash relay assault that funneled logins to the consumer accounts by way of one of many botnet units. Microsoft offered a diagram of the assault pictured under:
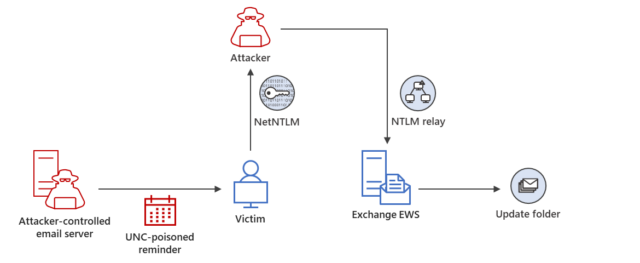
Microsoft
Development Micro noticed the identical botnet getting used to ship spam with pharmaceutical themes which have the hallmarks of what’s generally known as the Canadian Pharmacy gang. One more group put in malware generally known as Ngioweb on botnet units. Ngioweb was first discovered in 2019 operating on routers from DLink, Netgear, and different producers, in addition to different units operating Linux on prime of x86, ARM, and MIPS {hardware}. The aim of Ngioweb is to supply proxies people can use to route their on-line actions by way of a collection of recurrently altering IP addresses, notably these positioned within the US with reputations for trustworthiness. It’s not clear exactly who makes use of the Ngioweb-powered service.
The Development Micro researchers wrote:
Within the particular case of the compromised Ubiquiti EdgeRouters, we noticed {that a} botnet operator has been putting in backdoored SSH servers and a set of scripts on the compromised units for years with out a lot consideration from the safety business, permitting persistent entry. One other menace actor put in the Ngioweb malware that runs solely in reminiscence so as to add the bots to a commercially out there residential proxy botnet. Pawn Storm almost certainly simply brute pressured the credentials of the backdoored SSH servers and thus gained entry to a pool of EdgeRouter units they might abuse for numerous functions.
The researchers offered the next desk, summarizing the botnet-sharing association amongst Pawn Storm and the 2 different teams, tracked as Water Zmeu and Water Barghest:
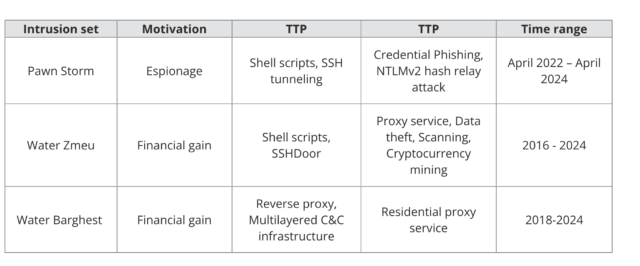
Development Micro
It’s unclear if both of the teams was accountable for putting in the beforehand talked about Moobot malware that the FBI reported discovering on the units. If not, that may imply routers had been independently contaminated by three financially motivated teams, along with Pawn Storm, additional underscoring the continuing rush by a number of menace teams to ascertain secret listening posts inside routers. Development Micro researchers weren’t out there to make clear.
The submit went on to report that whereas the January operation by the FBI put a dent within the infrastructure Pawn Storm trusted, authorized constraints prevented the operation from stopping reinfection. What’s extra, the botnet additionally comprised digital public servers and Raspberry Pi units that weren’t affected by the FBI motion.
“Which means that regardless of the efforts of legislation enforcement, Pawn Storm nonetheless has entry to many different compromised belongings, together with EdgeServers,” the Development Micro report mentioned. “For instance, IP deal with 32[.]143[.]50[.]222 was used as an SMB reflector round February 8, 2024. The identical IP deal with was used as a proxy in a credential phishing assault on February 6 2024 towards numerous authorities officers all over the world.”



