
Getty Pictures
Google’s Risk Evaluation Group confirmed Wednesday that they noticed a menace actor backed by the Iranian authorities focusing on Google accounts related to US presidential campaigns, along with stepped-up assaults on Israeli targets.
APT42, related to Iran’s Islamic Revolutionary Guard Corps, “constantly targets high-profile customers in Israel and the US,” the Risk Evaluation Group (TAG) writes. The Iranian group makes use of hosted malware, phishing pages, malicious redirects, and different ways to realize entry to Google, Dropbox, OneDrive, and different cloud-based accounts. Google’s TAG writes that it reset accounts, despatched warnings to customers, and blacklisted domains related to APT42’s phishing makes an attempt.
Amongst APT42’s instruments had been Google Websites pages that gave the impression to be a petition from legit Jewish activists, calling on Israel to mediate its ongoing battle with Hamas. The web page was original from picture information, not HTML, and an ngrok redirect despatched customers to phishing pages once they moved to signal the petition.
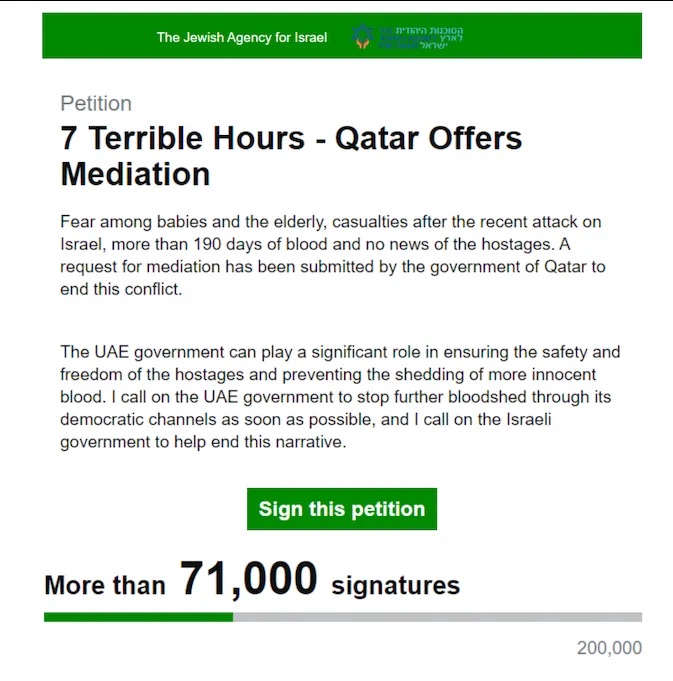
A petition purporting to be from The Jewish Company for Israel, searching for assist for mediation measures—however signatures quietly redirect to phishing websites, in response to Google.
Within the US, Google’s TAG notes that, as with the 2020 elections, APT42 is actively focusing on the non-public emails of “roughly a dozen people affiliated with President Biden and former President Trump.” TAG confirms that APT42 “efficiently gained entry to the non-public Gmail account of a high-profile political advisor,” which can be longtime Republican operative Roger Stone, as reported by The Guardian, CNN, and The Washington Publish, amongst others. Microsoft individually famous final week {that a} “former senior advisor” to the Trump marketing campaign had his Microsoft account compromised, which Stone additionally confirmed.
“In the present day, TAG continues to look at unsuccessful makes an attempt from APT42 to compromise the non-public accounts of people affiliated with President Biden, Vice President Harris and former President Trump, together with present and former authorities officers and people related to the campaigns,” Google’s TAG writes.
PDFs and phishing kits goal each side
Google’s publish particulars the methods wherein APT42 targets operatives in each events. The broad technique is to get the goal off their electronic mail and into channels like Sign, Telegram, or WhatsApp, or presumably a private electronic mail tackle that won’t have two-factor authentication and menace monitoring arrange. By establishing belief by means of sending legit PDFs, or luring them to video conferences, APT42 can then push hyperlinks that use phishing kits with “a seamless movement” to reap credentials from Google, Hotmail, and Yahoo.
After gaining a foothold, APT42 will typically work to protect its entry by producing application-specific passwords contained in the account, which usually bypass multifactor instruments. Google notes that its Superior Safety Program, meant for people at excessive danger of assault, disables such measures.
Publications, together with Politico, The Washington Publish, and The New York Instances, have reported being supplied paperwork from the Trump marketing campaign, probably stemming from Iran’s phishing efforts, in an echo of Russia’s 2016 focusing on of Hillary Clinton’s marketing campaign. None of them have moved to publish tales associated to the paperwork.
John Hultquist, with Google-owned cybersecurity agency Mandiant, instructed Wired’s Andy Greenberg that what seems initially like spying or political interference by Iran can simply escalate to sabotage and that each events are equal targets. He additionally mentioned that present fascinated with menace vectors could have to develop.
“It’s not only a Russia downside anymore. It is broader than that,” Hultquist mentioned. “There are a number of groups in play. And we now have to maintain an eye fixed out for all of them.”


