
Getty Photographs
Menace actors carried out zero-day assaults that focused Home windows customers with malware for greater than a 12 months earlier than Microsoft mounted the vulnerability that made them attainable, researchers mentioned Tuesday.
The vulnerability, current in each Home windows 10 and 11, causes units to open Web Explorer, a legacy browser that Microsoft decommissioned in 2022 after its ageing code base made it more and more prone to exploits. Following the transfer, Home windows made it tough, if not unimaginable, for regular actions to open the browser, which was first launched within the mid-Nineteen Nineties.
Methods outdated and new
Malicious code that exploits the vulnerability dates again to at the very least January 2023 and was circulating as not too long ago as Might this 12 months, in accordance with the researchers who found the vulnerability and reported it to Microsoft. The corporate mounted the vulnerability, tracked as CVE-2024-CVE-38112, on Tuesday as a part of its month-to-month patch launch program. The vulnerability, which resided within the MSHTML engine of Home windows, carried a severity score of seven.0 out of 10.
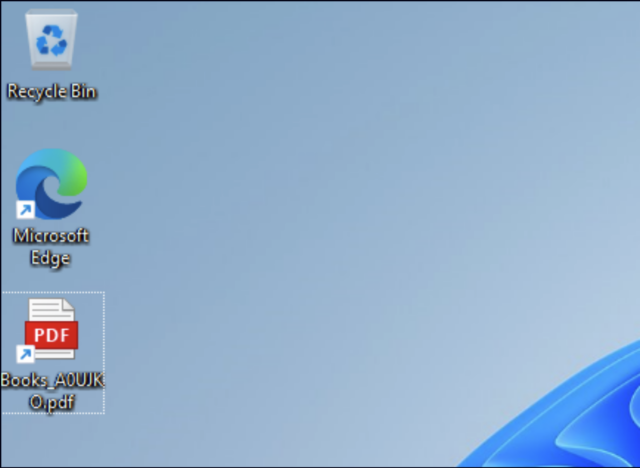
The researchers from safety agency Examine Level mentioned the assault code executed “novel (or beforehand unknown) tips to lure Home windows customers for distant code execution.” A hyperlink that appeared to open a PDF file appended a .url extension to the top of the file, for example, Books_A0UJKO.pdf.url, present in one of many malicious code samples.
When seen in Home windows, the file confirmed an icon indicating the file was a PDF slightly than a .url file. Such information are designed to open an software laid out in a hyperlink.
Examine Level
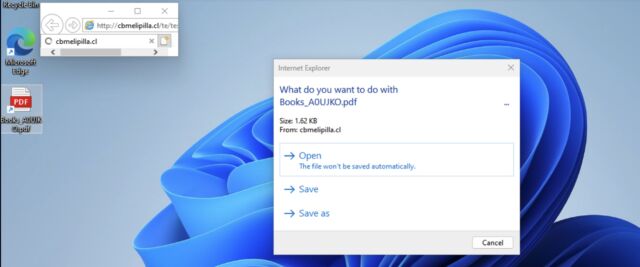
A hyperlink within the file made a name to msedge.exe, a file that runs Edge. The hyperlink, nonetheless, included two attributes—mhtml: and !x-usc:—an “outdated trick” risk actors have been utilizing for years to trigger Home windows to open functions similar to MS Phrase. It additionally included a hyperlink to a malicious web site. When clicked, the .url file disguised as a PDF opened the positioning, not in Edge, however in Web Explorer.
“From there (the web site being opened with IE), the attacker may do many unhealthy issues as a result of IE is insecure and outdated,” Haifei Li, the Examine Level researcher who found the vulnerability, wrote. “For instance, if the attacker has an IE zero-day exploit—which is way simpler to search out in comparison with Chrome/Edge—the attacker may assault the sufferer to achieve distant code execution instantly. Nonetheless, within the samples we analyzed, the risk actors didn’t use any IE distant code execution exploit. As an alternative, they used one other trick in IE—which might be not publicly recognized beforehand—to the most effective of our data—to trick the sufferer into gaining distant code execution.”
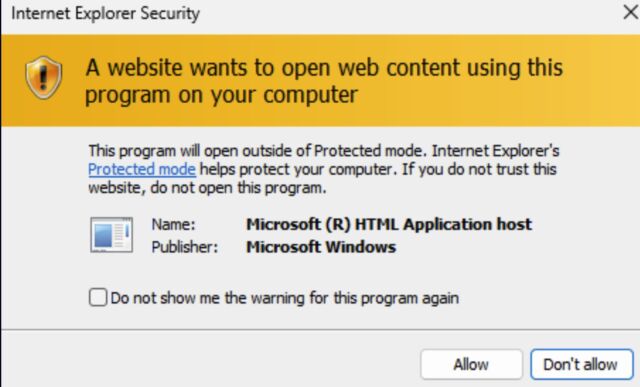
IE would then current the consumer with a dialog field asking them in the event that they needed to open the file masquerading as a PDF. If the consumer clicked “open,” Home windows offered a second dialog field displaying a obscure discover that continuing would open content material on the Home windows machine. If customers clicked “permit,” IE would load a file ending in .hta, an extension that causes Home windows to open the file in Web Explorer and run embedded code.
Examine Level
Examine Level
“To summarize the assaults from the exploitation perspective: the primary method utilized in these campaigns is the “mhtml” trick, which permits the attacker to name IE as an alternative of the safer Chrome/Edge,” Li wrote. “The second method is an IE trick to make the sufferer imagine they’re opening a PDF file, whereas actually, they’re downloading and executing a harmful .hta software. The general objective of those assaults is to make the victims imagine they’re opening a PDF file, and it’s made attainable through the use of these two tips.”
The Examine Level submit consists of cryptographic hashes for six malicious .url information used within the marketing campaign. Home windows customers can use the hashes to verify if they’ve been focused.





